But when there is a 70 alert i get alerted twice because of 70 and also 60 usage.
Splunk query time range.
Time the timestamp for the event.
Date and time functions.
A time range that you specify in the search bar or in a saved search overrides the time range that is selected in the time range picker.
The splunk web interface displays timeline which indicates the distribution of events over a range of time.
So there are alerts at 70 80 90.
The following list contains the functions that you can use to calculate dates and time.
When events are indexed the timestamp in the event is extracted.
For information about using string and numeric fields in functions and nesting functions see evaluation functions.
Open the time range picker.
For earliest type 2 in the field and select days ago from the drop down list.
The below screen shows various preset timeline options.
To run a search over the last two days select the relative time range option.
There are preset time intervals from which you can select a specific time range or you can customize the time range as per your need.
Event the raw event data.
Hi i have alerts when the number goes above certain of the disk usage.
You can use the relative option to specify a custom time range.
Select beginning of today.
On clicking on the search reporting app we are presented with a search box where we can start our search on the log data that we uploaded.
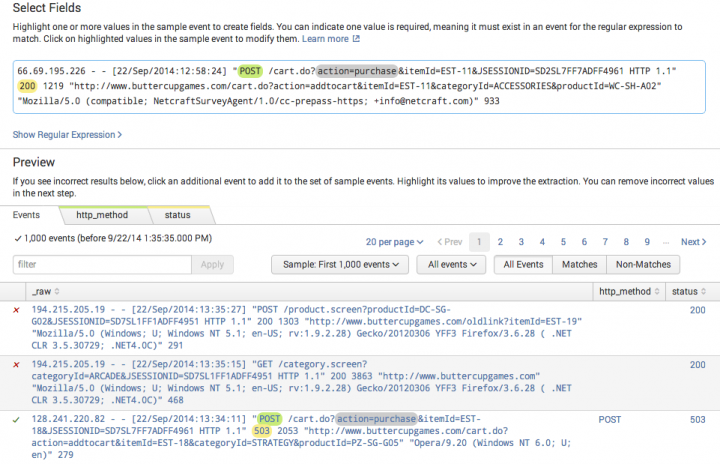
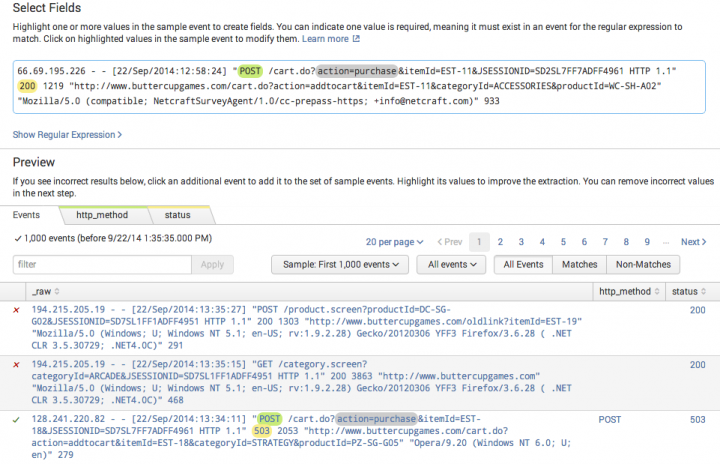
The selected fields from the fields sidebar appear at the bottom of each event.
For latest the default is now.
If the event does not contain a timestamp the indexing process adds a timestamp that is the date and time the event was indexed.
Communicator 05 11 2012 02 22 am.
Hello splunkers i have an iis log that i am testing against and i have a need to test for a specified range the time field in the log is formatted like this 2020 08 23t21 25 33 437 0400 2020 08 23t21 25 33 437 0400 i want to query everything between 21 25 33 and 21 25 43 2020 08 23t21 25 33 437.
Splunk splunk turn data into doing data to everything and d2e are trademarks or registered.
Splunk has a robust search functionality which enables you to search the entire data set that is ingested.
This feature is accessed through the app named as search reporting which can be seen in the left side bar after logging in to the web interface.
Change search query by time range philip wong.
In addition to the functions listed in this topic there are also variables and modifiers that you can use in searches.
For my case i want to query 24 hours data from original index and.
I am trying to keep the alert segmented to query the n.
Searching the time and fields when an event is processed by splunk software its timestamp is saved as the default field time.
Can i create a dashboard that the searches depend on time range selected.